On a public blockchain, nothing really disappears. Transactions stay visible. Wallet addresses, amounts, timestamps—anyone can pull them up. The code is not the problem.
What trips people up is how they use it. Sending funds at the same time every week. Reusing wallets. Moving money through the same exchange accounts. Little patterns build up. Once those patterns show up, separating activity becomes harder than people expect. What looked unrelated starts to line up.
And most of the time, this does not require advanced tracking software. Basic data and a bit of patience are often enough. Metadata fills in the gaps, and network analysis does the rest.
Metadata Tells the Real Story
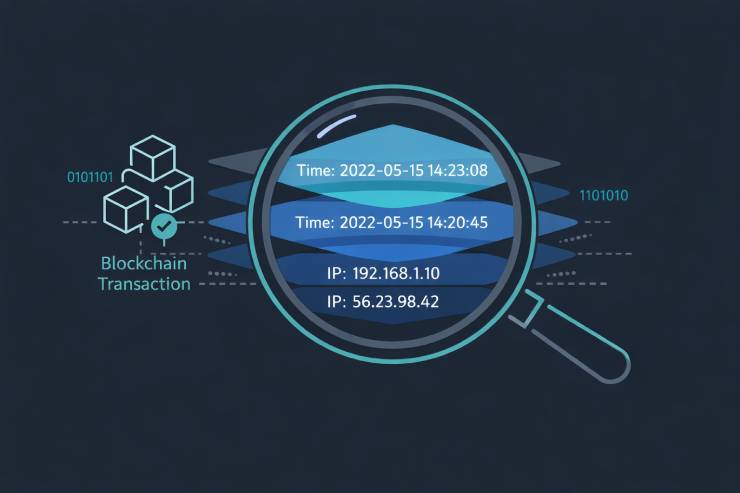
Transaction data shows the transfer. Metadata shows everything else. Timing patterns indicate time zones. Gas fee choices reflect urgency or automation. Reused deposit addresses connect separate wallets.
IP-level interactions before broadcast can leak location data. Wallet software sometimes embeds version information. These technical details accumulate into behavioral profiles that analytics firms use to build comprehensive user maps.
When multiple addresses send funds into one wallet during a single transaction, common ownership becomes obvious. Changing the address reuse strengthens the link. Analytics tools track these patterns automatically through statistical clustering.
Blockchain forensics companies publish detailed case studies showing exactly how funds get tracked. CCN regularly covers enforcement actions where prosecutors traced cryptocurrency through supposedly anonymous networks. Their reporting demonstrates that exposure builds gradually through wallet clustering, exchange deposits, and predictable transaction schedules rather than single catastrophic mistakes. These documented cases prove blockchain transparency works against users who assume addresses alone provide anonymity.
Exchange Connections Break Isolation
KYC requirements tie real identities to wallet addresses. One verified withdrawal links blockchain activity to government documents. Clustering algorithms extend that connection to related wallets.

Exchanges maintain detailed records. Withdrawal addresses get logged with timestamps and amounts. When law enforcement requests data, exchanges provide complete transaction histories tied to verified identities.
Regular transfers between the same addresses create obvious patterns. Consistent amounts and timing make connections easier to prove. Round numbers suggest manual transfers. Irregular decimals indicate automated systems.
Spreading funds across multiple wallets helps only if those wallets never interact. Most users merge funds for convenience or send small amounts between wallets to test connectivity. Each interaction adds evidence.
Network Analysis Creates User Profiles
Activity patterns build behavioral fingerprints. A wallet that consistently interacts with DeFi protocols between 6 PM and midnight EST suggests location and schedule. Participation in niche NFT markets or specialized tools reveals specific interests. Gas price tolerance demonstrates financial sophistication.
Each transaction adds detail. The logic matches web tracking—browsing history over months exposes far more than individual cookies. Analysts build psychological profiles from transaction choices. Risk tolerance shows in leverage positions. Patience appears in holding periods.
Public ledgers function as analyzable databases. Machine learning models identify patterns humans would miss. Network graphs visualize connection clusters.
Cross-Chain Activity Multiplies Exposure
Using multiple blockchains creates more data points, not better privacy. Bridge transactions leave timestamps on both chains. Liquidity pool participation generates on-chain records. Staking shows asset management behavior. Every cross-chain operation multiplies the available metadata.
Analysts compare timing between outgoing and incoming transfers across networks. A wallet sending 10 ETH through a bridge at 3:47 PM followed by 9.95 ETH appearing on another chain at 3:49 PM creates an obvious connection. The two-minute gap accounts for bridge processing time. Similar amounts minus fees strengthen the link.
The more chains involved, the more metadata exists. Cross-chain operations add connection points rather than obscuring them. DeFi protocols often require multiple approvals and interactions. Each step leaves traces. Complex strategies generate more data than simple holding.
Privacy Tools Require Operational Discipline
Mixing services and privacy coins reduce traceability when used correctly. Poor implementation negates their effectiveness completely. Sending mixed funds directly to verified exchanges defeats the purpose. The mixing created temporary obscurity, but the exchange deposit reconnects everything.
Mixing once and then repeating identical patterns exposes the connection. The pattern matters more than individual transactions. Using the same wallet for multiple functions creates linkable activity. Mixing coins used for trading alongside coins used for purchases leaves obvious trails.
Regulatory scrutiny continues increasing. Some mixing services face monitoring. Others face sanctions. Tornado Cash faced legal action despite legitimate use cases. Authorities monitor known mixing services and flag interactions. Privacy tools work only with consistent operational security maintained over long periods.
Routine Behavior Creates the Biggest Leaks
Most identity exposure comes from everyday actions. Trading and social media on the same device leaves cross-contaminated data. Wallet software accesses the same IP address as email clients.
Exchange logins from identifiable IP addresses create permanent records. VPN disconnections expose real locations. Home internet connections tie activity to physical addresses.
When someone shares a wallet address in public, the privacy layer thins out fast. It might seem harmless. A donation link in a bio. An address in a forum signature. A crowdfunding page collecting crypto.
But once that address is tied to a name, handle, or profile, the trail is open. Every past and future transaction connected to it becomes easier to map back to a real person. Transaction hashes shared for support requests enable tracking.
Fund transfers immediately after public statements create timing correlations. Announcing investments and then moving funds minutes later links the wallet to the statement. Online traces intersect constantly. Email addresses used for exchange accounts appear in data breaches. Crypto transactions represent one piece of a larger digital footprint.
Practical Privacy Measures
Complete anonymity remains unlikely on public chains. Risk reduction stays achievable through careful planning:
Separate wallets by function rigorously. Storage addresses should never interact with trading addresses. Create distinct wallets for different purposes. Never consolidate them.
Avoid consolidating funds without clear justification. Every merge transaction creates clustering evidence. If consolidation becomes necessary, use privacy tools correctly and wait a substantial time between steps.
Limit repeated transfers between the same addresses. Vary amounts and timing when possible. Round numbers suggest manual control. Irregular decimals indicate automation.
Withdraw from KYC exchanges carefully. Those transactions connect verified identity to blockchain addresses permanently. Consider using intermediate wallets before moving to final destinations. Wait varying time periods between hops.
Use dedicated devices or network setups for different activities. Physical separation provides stronger guarantees than software isolation. Privacy means making connections harder to establish, not achieving invisibility.
The Transparency Trade-off
Open ledgers enable transactions without intermediaries and support global access to programmable financial tools. Transparency prevents many fraud types and simplifies verification. These represent core advantages of digital innovation in finance.

That same openness limits privacy. Users benefit from transparency while accepting its consequences. Understanding this trade-off shapes realistic usage strategies.
Strategy Over Assumption
Wallet addresses look anonymous because names stay hidden. But anonymity depends on whether activity can be linked, not on missing labels. Metadata, timing patterns, and clustering analysis make those connections possible.
Public blockchains operate transparently by design. Privacy requires operational discipline sustained over time. Each transaction adds to visible patterns. Assuming automatic anonymity leads to exposure through accumulated mistakes.
Understanding metadata provides the foundation for realistic privacy strategies. Blockchain records stay permanent. Privacy depends on consistent practice rather than default protections.











