Linux enthusiasts like to put resilience in the face of different threats as one of the operating system’s most impactful advantages. Few hackers bother to write viruses for Linux environments, while security features like SELinux make unauthorized resource access especially difficult.
You might have heard about SELinux before but aren’t sure what it is or what its role is in maintaining Linux security. Wonder no longer exists since this article offers everything you’ll need to understand its principles.
What is SELinux?
SELinux, or Security-Enhanced Linux, is an access control module that integrates at the kernel level. National Security Agency (NSA) was the first to develop it in collaboration with Red Hat, but other contributors continue to update it due to Linux’s open-source nature. It’s one of two popular managed access control (MAC) modules, the other being AppArmor.
Red Hat has taken the reins of SELinux development, so, unsurprisingly, secure distros like CentOS, Fedora, RHEL, and AlmaLinux come with it by default. These distributions cater to various users’ needs, especially developers who require robust environments to develop and deploy applications securely. While AppArmor is a viable alternative, SELinux offers more in-depth protection options, albeit at the cost of complexity.
What is SELinux’s Role in Linux Security?
The intricacies of SELinux fortify Linux against threats, similar to how smart technology needs to balance user convenience with privacy. It shields system resources like files, ports, and processes from access attempts by actors who don’t have the required permissions. This is exceptionally useful in preventing attackers from causing widespread system damage if they manage to find a security vulnerability.
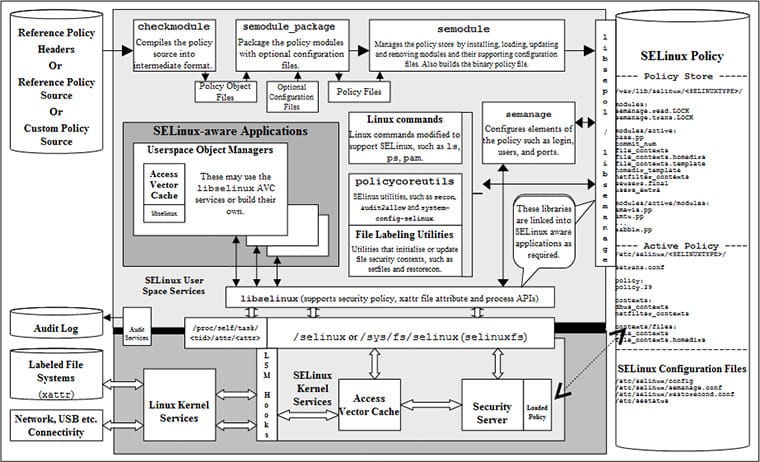
Access control is mandatory, meaning every user or process that wants access privileges goes through an inspection first. They can proceed only if they satisfy the conditions outlined in the access policy for a specific app or service stored in the security server.
A subject needs to request access to a resource – or object – first. A manager in charge of the object then consults the security server, which resides on the kernel level. The subject gains access if its privilege and access level satisfy the rule requirements for a given app or service’s policy. Finally, the Access Vector Cache (AVC) stores each decision the security server makes to execute it faster next time.
Deep Security Integration
SELinux plays a crucial role beyond mere access control. This deep integration helps to create a robust security posture, which is essential not only for system processes but also as we increasingly rely on complex algorithms and data-driven applications that must operate within secure parameters.
This deep integration helps create a robust security posture where policies strictly govern the behavior of processes and system calls, thus limiting the potential attack vectors that can be exploited due to system misconfigurations or vulnerabilities. Integrating security within the kernel offers a reliable enforcement mechanism, operating with fine-grained controls to confine system processes, enhance isolation, and prevent privilege escalation.
A Matter of Context
Now you know what SELinux is, but how does it determine the outcomes of interactions between users or processes on one end and resources on the other? That’s where ‘context’ comes in.
Context in an SELinux setting is a label assigned to every user, port, file, directory, etc. It’s a label consisting of four parts that must be compatible before gaining access.
User
The first part of the label identifies the user SELinux associates with a resource. While they’re generated based on all the regular users on a computer or network, SELinux users are a separate category. You can’t create additional ones while SELinux is running.
Role
This part denotes a user’s current role in the system. For example, a database administrator could log on as such, but they could also log on as a regular user. The first part of the context – their unique user identifier – would be the same in both instances. The second part would differ based on the current role and likely come with different privileges.
Type
A resource’s type is the main part of its context. It defines what kind of object you’re dealing with and distinguishes between different ones, like files and directories. SELinux uses types to set access rules and define policies.
Range
Range is the last and optional part of a context. It’s useful for categorizing resources based on sensitivity. You can also use range to define which categories they apply to and further restrict the availability of certain resources.
What Modes Does SELinux Operate In?
There are three modes you can set SELinux. You can disable or enable SELinux, which operates in Permissive or Enforcing modes.
Disabled is self-explanatory. Admins might not want to bother with SELinux since it causes conflicts with some popular programs.
All Linux versions use Discretionary Access Control (DAC) as the basis for handling permissions. Setting SELinux to Permissive mode will comply with the DAC’s policies while logging actions or any warnings the MAC might have issued. Permissive mode is useful as a diagnostics tool when you’re first setting SELinux up or for troubleshooting and conflict resolution.
Enforcing mode indicates SELinux is completely active and will enforce policies and permissions as outlined in the security server.
SELinux in a Broader Cybersecurity Context
While running SELinux brings tangible benefits for Linux system security, limitations exist. It’s an excellent tool for monitoring, controlling, and fine-tuning user and app permissions. However, you’ll still want to install a solution to guard against harmful and exploitative code like antivirus or antimalware tools. You can read more about the difference between antivirus and antimalware to find something more suitable for your needs.
You should also remember to use other essential security tools, especially when connecting to the internet. That is because SELinux doesn’t facilitate connection security in any way. A password manager suitable for Linux should do the job of securing credentials.
Moreover, companies running Linux-based servers would still need a secure way for remote employees to connect to their internal networks, and a virtual private network remains the choice solution in such situations. Their encrypted tunnels ensure users can interact with sensitive resources safely while remaining anonymous and untraceable.
Practical SELinux Policy Management
SELinux policies are not static; they require careful crafting and continuous management to align with evolving system exigencies. Policies are typically composed of type enforcement files (.te), which articulate the rules and permissions, interface files (.if), which act as functional contracts between elements, and file context files (.fc) that map file paths to security contexts.
Managing these policies involves creating new modules or adjusting existing ones to align with system demands, emphasizing SELinux policy management’s dynamic yet structured nature. Configuring WordPress on a Linux server is a prime example where SELinux policies can enhance security during setup.
Conclusion
Consider a scenario in a corporate server environment, where data integrity is of utmost importance. Here, SELinux is used to prevent a web server from accessing critical financial records directly. A policy is defined where the web server, tagged as httpd_t, can only interact with files marked as httpd_sys_content_t. Financial records located in the directory with the type financial_records_t are off-limits.
Any unauthorized access attempt by the web server, even if the traditional Unix permissions allow it, is blocked by SELinux. This ensures strict separation of duties where only authorized services, such as a dedicated financial application running with the appropriate context label, can access these sensitive files.
SELinux is a complex and technical aspect of Linux, not many users bother mastering. It still could use some additional measures to be intact, but even by using it solely, you could improve your security game many times. We hope that by finding out more about it, you’ll consider enabling SELinux and using it to enforce its security and individual component independence.










