It’s no secret than online privacy and anonymity has become a hotly debated topic in recent times, and with good reason. It makes a lot of sense to be concerned about these issues given that an increasingly large part of our daily lives revolves around technology and the internet. Between big corporations and government organizations trying to collect personal data for their own purposes and cyber criminals constantly on the hunt for easy prey, it can sometimes be unnerving to surf the internet. Or at least some parts of it.
But while there are certainly many threats in the digital space these days, there are also plenty of tools you can use to protect yourself. VPNs and proxy servers are pretty obvious solutions, as are antimalware software and secure web browsers like Tor. But an even more secure solution that you may have overlooked until now is Linux. MacOS is often praised for offering pretty good protection against malware and hackers, however, no other operating system can hold a candle to Linux when it comes to overall system security.
Linux lets you transfer files securely via SFTP, lets you secure connections with SSH, gives you access to a lot of remote desktop clients, and so much more. But as with everything that has to do with Linux, some distros are better than others in certain areas and security is no exception. With that in mind, we decided to make your hunt for the safest distribution easier by putting together a list of the best and most secure Linux distros for privacy and security.
1. Qubes OS
- Uses virtual machines to compartmentalize apps
- Great integration with Whonix and the Tor network
- Primarily targeted at advanced users
Qubes OS is a popular Fedora-based distro that touts itself as being “a reasonably secure operating system.” That’s a pretty modest claim, however, as most users would tell you that the distro is actually among the best of its kind. One of the highlights of Qubes OS is a compartmentalization feature that isolates every application you’re running and places it into its own virtual environment. This means that even if you were to download malware by accident, it wouldn’t be able to affect your personal files. Furthermore, all data gets automatically deleted at the end of each session, which adds an extra level of security to your system.
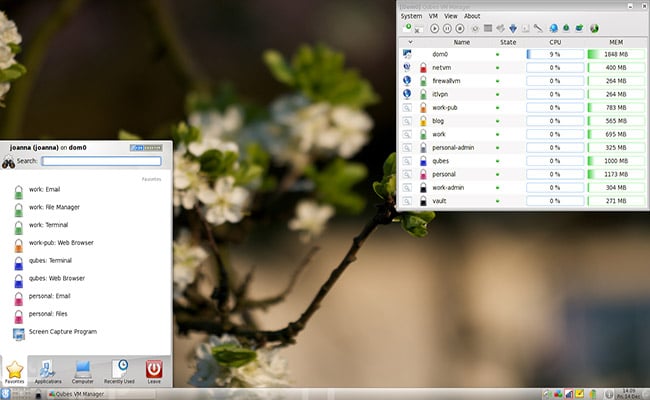
The distro has excellent integration with Whonix, a piece of software that can anonymize everything you do online. Whonix relies on the Tor network but uses a few other technologies in order to boost security. Famous whistleblower Edward Snowden claimed back in 2019 that he uses Qubes paired with a Whonix gateway on a daily basis. That says a lot about why he and so many other people see Qubes OS as being one of the most secure Linux distros available today. But, as Snowden also pointed out, the distribution requires a fairly high level of technical knowledge. If you’re still a novice, you’re better off trying a few beginner-friendly Linux distros before jumping into Qubes.
Setting up Qubes OS on your own can be a bit tricky even if you’re an experienced user so we recommend checking out the guides found on the official website. Among other things, you will find information on how to build templates for other desktop environments and base distros, just in case you’re not a fan of the default one. A few other options include Ubuntu, Arch Linux, CentOS, Xfce, and Debian. However, keep in mind that some of these templates were created by the community and are not maintained directly by the developers of Qubes OS.
Minimum system requirements:
- 64-bit Intel or AMD CPU
- 4GB of RAM
- 32GB of storage
Latest stable version: 4.0.3
2. Tails Linux
- Designed to run in “Live” mode
- Comes bundled with very useful applications
- Complete anonymity while browsing the internet.
Initially launched more than a decade ago, Linux Tails remains one of the best and most secure Linux distros around. The distribution is based on Debian and its name is an acronym that stands for The Amnesic Incognito Live System. Just as its name indicates, Tails can run in Live mode off a DVD or USB stick allowing you to go about your business without installing anything locally. And, more importantly, without leaving any trace of your activities. Tails can also run in persistent mode but you’ll need an encrypted USB if you want to store data in a secure manner.
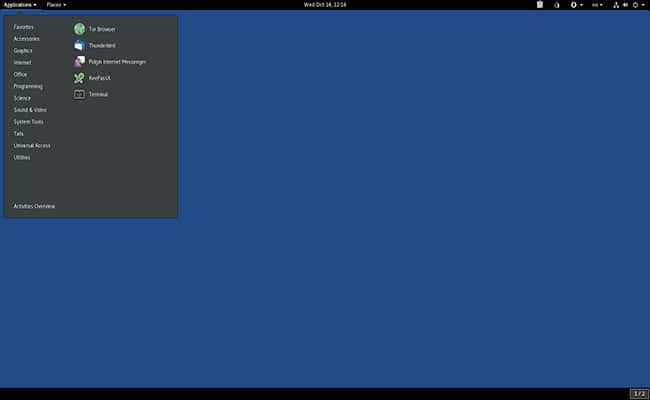
Tails comes bundled with a handpicked selection of applications designed to keep you anonymous while you’re working on sensitive documents. A few examples include KeePassXC, which lets you create and store strong passwords, Thunderbird with Enigmail, which lets you send encrypted emails, OnionShare, which is used to share files over the Tor network, and more. Of course, you also get the Tor Browser to go along with all of that and the uBlock ad-blocker is available as an extra bonus.
Interestingly enough, Tails automatically blocks any application that tries to connect to the internet without going through the Tor network first. As an added safety measure, the OS doesn’t write anything to the hard disk, using your RAM as a temporary storage solution instead. Tails also comes with built-in tools designed to prevent websites from tracking your location or collecting your private data. But on the off chance that a website does manage to track you, Tails makes it easy to change your identity and location at any time.
Minimum system requirements:
- 64-bit CPU
- 2GB of RAM
- 8GB USB stick
Latest stable version: 4.8
3. Kali Linux
- A great choice for cybersecurity experts
- Free courses on ethical hacking
- Comes bundled with hundreds of pen-testing tools
Kali is another Debian-based distribution designed with security in mind. But unlike some of the other distros on this list, Kali is primarily used for offensive rather than defensive operations. A few popular use cases for Kali Linux include penetration testing, computer research, security research, and reverse engineering. The distro is an excellent choice for exploiting vulnerabilities, probing for potential weaknesses in the system, surveying IP addresses, and even breaching firewalls. There are over 600 penetration testing tools included right off the bat, with more available to install manually.

Some of the pen-testing tools bundled with the OS include fan-favorites like Wireshark, Ettercap, Maltigo, Kismet, and more. Then, you’ve also got things like Armitage, a tool that allows you to launch cyberattacks in order to test the security of a system. If you don’t want to feel overwhelmed by all the tools offered by the distro, you can simply install metapackages instead. These are subsets of tools designed for specific purposes. Among other things, you can find a desktop manager metapackage. The default desktop environment is Gnome but you can change it to Mate, Xfce, KDE Plasma, LXDE, and a few other options.
Kali Linux’s impressive range of tools makes it popular with many white hat hackers and cybersecurity experts. If you’re looking to pursue a career in ethical hacking, Kali is definitely a good place to start. The best part is that you can enroll in the Kali Linux Dojo for free workshops and training courses where you can hone your skills. In addition to the free courses, you can also find paid ones that will help you take your skills to the next level. The paid courses aren’t exactly cheap but they are definitely worth the asking price in our opinion.
Minimum system requirements:
- 64-bit CPU
- 1GB of RAM (2GB recommended)
- 2GB of storage (20GB recommended for full install)
Latest stable version: 2020.2
4. Parrot OS
- Good for practicing white-hat hacking
- Comes bundled with lots of pen-testing tools
- Also works well as a regular distro for daily use
Parrot OS is a very secure Linux distro created by the Parrot Project, which is comprised of developers and specialists from all over the world. The goal of the project is to build a shared framework of tools centered around security, privacy, and defending against cyber threats. Parrot OS uses Debian as its base and comes bundled with a suite of utilities that can be used for everything from pen-testing to reverse engineering and more. The suite also includes a number of tools that allow users to create and customize their own software.

Just like Kali, Parrot OS is a particularly good choice for those who want to practice ethical hacking or test their own systems for any potential vulnerabilities. There are quite a few defensive tools you can employ to help thwart cybercriminals but, for the most part, this is an offensive distro. It is worth noting, however, that the distro is available in multiple versions and some of them don’t include a lot of tools right off the bat. Make sure to download one of the “Security” editions if you want to get the most out of Parrot OS. You can also grab a version of the distro that only includes basic applications like OnionShare and the Tor Browser. This gets you a very lightweight distro that you can customize to your liking.
Don’t want to replace your current operating system with Parrot? No problem. The distro can easily be installed on top of another operating system (including non-Linux operating systems) or you can even use it to run containers directly from a cloud environment. One of the drawbacks of Parrot is that it doesn’t offer a large selection of desktop environments to choose from. Namely, you’ll have to pick between Mate and KDE. Another thing you may need to worry about is possible stability issues because Parrot OS is based on the testing branch of Debian 10.
Minimum system requirements:
- Dual-core x86_64 CPU
- 2GB of RAM
- 20GB of storage (40GB recommended)
Latest stable version: 4.9.1
5. BlackArch Linux
- Comes bundled with more than 2500 tools
- Netinstall version takes up less than 500 MB
- Recommended for advanced users familiar with Arch Linux
As I’m sure you’ve noticed by now, some of the most secure Linux distros available at the moment are based on Debian. However, there are some exceptions. BlackArch, for example, is one of a handful of Arch-based distros that are heavily focused on security. BlackArch hasn’t been around for very long at this point but the distribution already managed to gather a very impressive number of penetration testing tools in its repository. We’re talking more than 2500 tools to choose from but you don’t have to worry about all of them at once because you can install them individually or in groups.
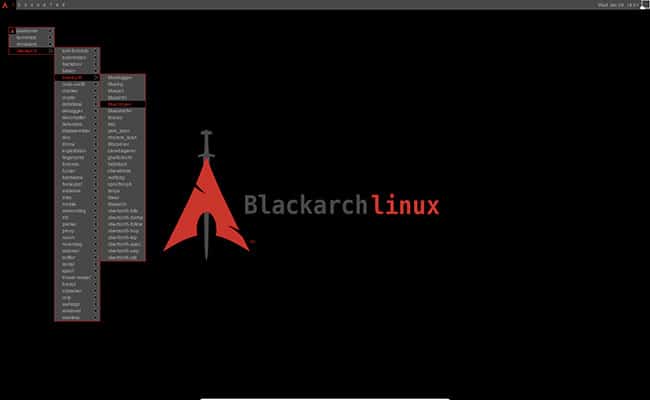
BlackArch is a very flexible distro that can be installed locally or booted from a live USB and it runs on pretty much everything, including microcomputers like the Raspberry Pi 4. That said, the default ISOs are pretty large so make sure to grab the Netinstall version if you want to use the distro on modest hardware. The bad news is that BlackArch doesn’t come with a user-friendly desktop environment so you’ll have to settle for working with a window manager. This, among other things, makes the distro difficult to recommend to beginners.
BlackArch Linux follows a stable release model where a brand new ISO is made available every four months. Software packages can be updated individually using the Pacman manager or by downloading them directly from the repository. If you want to do a base installation, you can go to the official website to find a list of all available tools. Combing through thousands of tools can be very time consuming so make sure to sort them by categories like “proxy”, “crypto” or “backdoor” in order to make your life a bit easier.
Minimum system requirements:
- 64-bit CPU
- 1GB of RAM
- 500MB of storage (15GB for full install)
Latest stable version: 2020.01.01
6. IprediaOS
- Uses both I2P and the Tor network for encryption
- Very modest system requirements
- Hasn’t been updated in a long time
IprediaOS is a secure Linux distro based on Fedora that works similar to Tails in many ways. The distribution runs all incoming and outgoing traffic through the Tor network and has an additional layer of security known as I2P. The I2P network ensures anonymous communication by encrypting all data and using a dynamic and distributed system, with no trusted parties. Some of the tools that come with the network include things like an anonymous BitTorrent client, anonymous IRC client, anonymous e-mail client, IP router, and more.
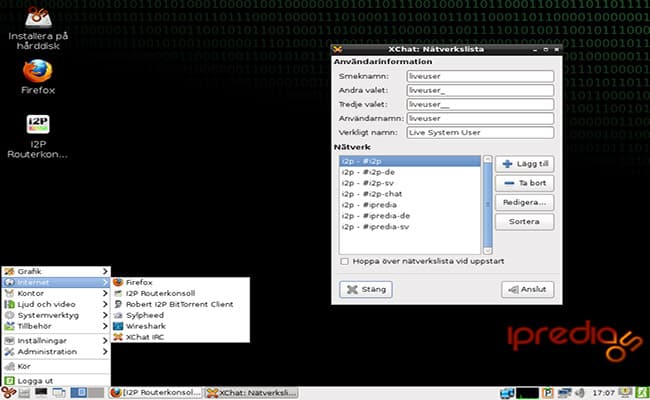
The I2P network uses a special method for routing traffic known as garlic routing or garlic encryption. This method is similar in many ways to the onion routing used by the Tor network, however, it has certain particularities that make it even more secure. This is because garlic routing involves creating encrypted unidirectional tunnels for communication, as opposed to established circuits. Each party creates separate tunnels for unbound and inbound traffic, which makes the flowing data more difficult to track.
While IprediaOS can be used for a wide variety of purposes, the distro excels when used to access “hidden services”. Uploading and downloading torrents are particularly popular uses cases for the distro. It helps a lot that IprediaOS can run in a virtual box and that its system requirements are so low that you can even install it on an old laptop. As you might expect, the distro is very minimalistic but it still looks nice enough thanks to the Gnome desktop environment.
Minimum system requirements:
- 400Mhz or better CPU
- 768MB of RAM (1GB recommended)
- 10GB of storage
Latest stable version: 0.9.6
7. Discreete Linux
- Designed to protect against surveillance
- Very effective against all types of spyware
- Still in Beta at the moment
This one is pretty self-explanatory. As you can already tell by the name, the distro is all about discretion and privacy. While the name may look like a typo, it’s actually a combination of two terms – discreet and discrete (detached, separated). The operating system is a continuation of the Ubuntu Privacy Remix project, however, the current iteration is based on Debian. Discreete was designed specifically to protect sensitive data against surveillance attacks, especially those coming from government organizations.
The goal behind the project was to create an isolated local working environment that can’t be accessed by Trojan software or any other type of spyware. Discreete uses a simple but effective method for achieving its goal that involves closing all entrances and exits of the system. If malicious software does somehow make it in, the distro also has various systems in place that can isolate it and prevent it from spreading to other parts of the system. To make the security even more robust, Discreete is a pure live distribution, meaning that you couldn’t install it on your machine even if you wanted to.
The fact that Discreete can’t be installed locally could be seen as a drawback by some, then again, the distro was designed with a very specific purpose in mind. The distro is meant to be used by journalists, whistleblowers, human rights defenders, political activists, and anyone else who could become a target of government surveillance. If you think your government might be spying on you, this distro could be the solution. But even if you don’t, Discreete is still worth looking into because of its solid privacy features. Keep in mind, though, that Discreete is still in Beta so it might not be entirely foolproof at this stage.
Minimum system requirements:
- i386 CPU or better
- 1GB of RAM
- 2GB of live storage
Latest stable version: Still in Beta
8. Linux Kodachi
- Very user-friendly compared to other distros
- Good selection of pre-installed security apps
- Uses RAM instead of disk space for temporary data storage
Most of the secure Linux distros currently available can be quite complicated to wrap your head around because they are primarily meant for advanced users. Luckily, there are a few exceptions like Kodachi that try to be accessible to everyone. After all, regular users need their privacy, too. Kodachi was designed with ease of use in mind and comes bundled with all the tools and applications you would expect from a traditional operating system. Plus many security-centric utilities, of course.

Linux Kodachi works similar to Tails in the sense that it temporarily stores important data in your RAM instead of your disk storage. This has multiple benefits but probably the most important one is that all trace of your activities is gone as soon as you shut off your computer or close the distro. Kodachi can be booted from a live USB drive, allowing you to quickly access the distro whenever you want. The distro is small enough to be stored on a DVD or SD card as well, however, it’s probably better to burn it onto a USB anyway because it will be easier to encrypt.
There are quite a few security tools you can play with if you decide to grab this distro, including Riot, VeraCrypt, Wire, Stacer, KeyPassXC, and many more. In addition, you can also find a lot of other applications that are commonly found on traditional operating systems, such as FileZilla, Audacity, or Shutter. I2P and the Tor network as both included as well, along with a VPN, secure browser, cryptographic tools, and various other utilities. Linux Kodachi can be considered a hybrid distro as it is based on both Xubuntu and Debian.
Minimum system requirements:
- 64-bit CPU
- 2GB of RAM
- 4GB of storage (30GB for full install)
Latest stable version: 7.1
9. TENS (Trusted End Node Security)
- Designed to be booted from a live USB or DVD
- Created by the US Air Force; approved by the NSA
- Modest system requirements
We covered quite a few distros designed to stop government agencies from spying on users but things sometimes work the other way around, too. Sort of. TENS is a secure Linux distro created by the United States Air Force and was approved by none other than the NSA. Some people might find this fact odd or even a bit suspicious but don’t worry because the NSA won’t use it to monitor your activities. It probably couldn’t even if it wanted to because TENS is a barebones Linux distro that’s meant to be booted off a live USB stick or CD/DVD.

TENS doesn’t require any administrator privileges and comes with a customizable firewall. You don’t have to install anything on your computer and all your activities are erased once you remove the storage media. One of the most interesting things about TENS is that it supports logging in via Smart Card. Using this option, the operating system can be used to access CAC and PIV-restricted US government websites. Needless to say, though, you probably don’t want to do that unless you have the necessary authorization.
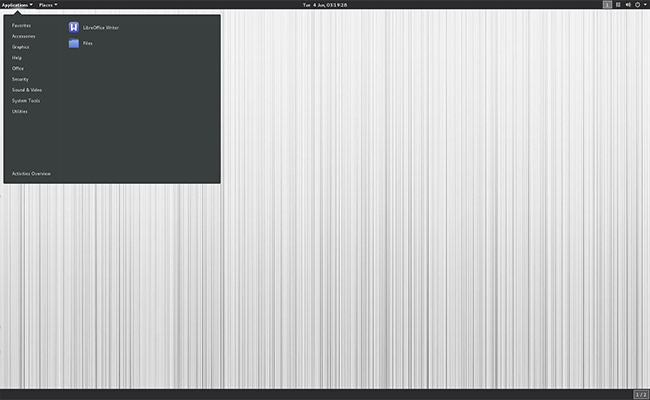
There are a couple of different versions of TENS you can download but not all of them are meant for the general public. Most users will want to stick to the TENS-Public or TENS-Public Deluxe editions. The two are pretty similar but the Deluxe version comes with some additional pieces of software, such as the LibreOffice suite. On the off chance, you’re working for a government organization, you’ll want to look into TENS-Professional, a more robust version of the distro that comes with a powerful encryption wizard and more customization options.
Minimum system requirements:
- Intel-based 64-bit CPU
- 1GB of RAM
- 1GB of live storage
Latest stable version: 3.0.1
10. Subgraph OS
- Uses a hardened kernel to boost security
- Great for protecting against system-wide attacks
- Relies heavily on the Tor network
Subgraph OS is a user-friendly and secure Linux distro that focuses on network-related security. The operating system also excels at stopping exploits, malware attacks, and many other similar activities that could harm your system. Subgraph OS comes equipped with an arsenal of powerful tools designed to stop system-wide attacks and prevent malware from spreading to important applications and processes on the off chance that someone does manage to infect your system.

Similar to Qubes OS, Subgraph runs applications in isolated environments inside a containment layer that sits on top of a hardened kernel. The hardened kernel was built using state-of-the-art security enhancements and incorporates a firewall, Metaproxy, and filesystem encryption. The developers included as few features as possible into the kernel in an attempt to reduce its attack surface. As far as the applications are concerned, there aren’t many that come pre-installed with the OS but you can expect common ones like a web browser, email client, video player, PDF viewer, the LibreOffice software suite, and more.
Just like most of the other distros, we covered in this article, Subgraph OS uses the Tor network in order to make things even more secure. By default, all applications that communicate outside the system are required to pass through Tor first. But there are certain exceptions, such as when trying to access a public Wi-Fi network for example. If needed, users can manually white-list applications and create additional exceptions. Before downloading the distro you should keep in mind that Subgraph OS is in the Alpha stage of development at the moment, which means that you’re pretty likely to run into certain stability issues.
Minimum system requirements:
- X86_64 CPU
- 1GB of RAM
- 3GB of storage
Latest stable version: Still in Alpha
Final Thoughts
Linux was conceived to be more secure than other operating systems, a fact that becomes immediately obvious regardless of which distro you use. But as it’s often the case with these things, some Linux distros are a lot more secure than others. Even among distributions designed specifically with security in mind, you can find different levels of reliability. For instance, all-purpose secure distros might not be as good at protecting against spyware or malware as distributions that focus entirely on those areas.
An important aspect that’s always worth keeping in mind when it comes to secure Linux distros is the ease of use. Or rather, the lack of it. Since these types of distributions are usually created for cybersecurity experts and white hat hackers, they tend to have a steeper learning curve than traditional operating systems. But if you can manage to wrap your head around one of these distros, chances are you’ll never have to worry about the security of your computer ever again.











Your pic is F’ing hillarious, Mr. Moth.